CURSE SATAN BEYBLADE BATTLE! Takara Tomy VS Flame (Real VS Fake) | Beyblade Burst Superking Sparking - YouTube

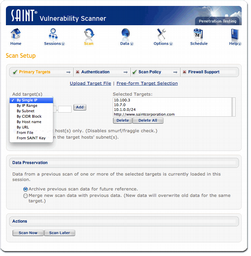
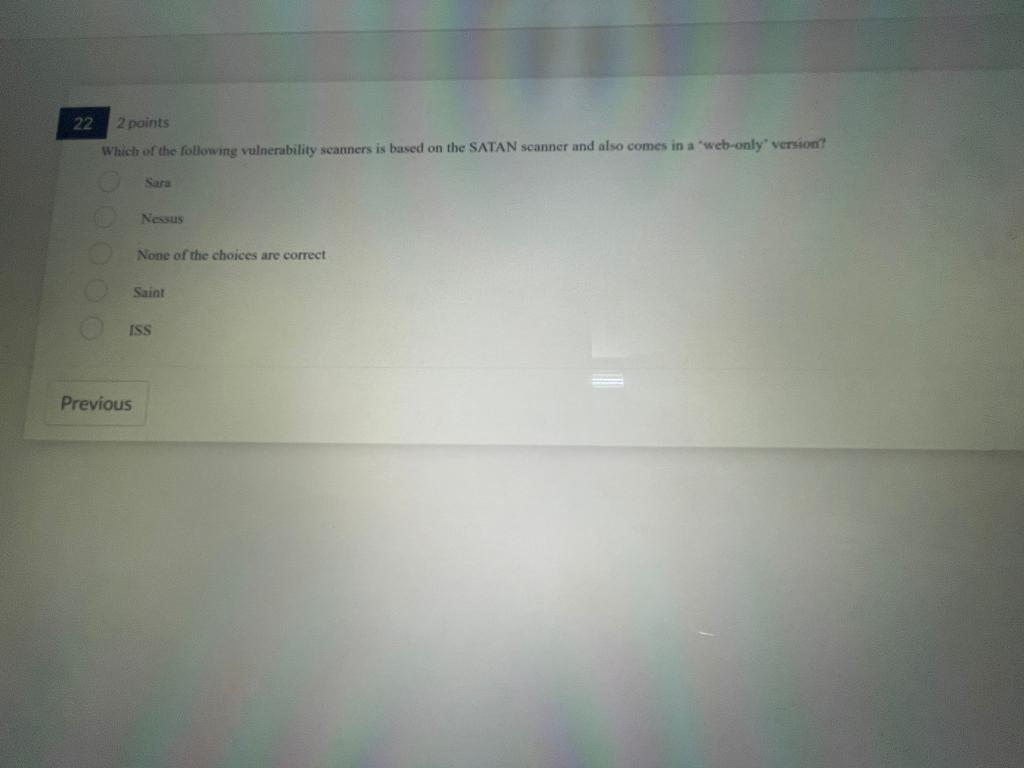
Bugs SATAN scans for It is interesting to look at the bugs SATAN scans for. They are easily detected by the scanners and therefore do not pose a threat. - ppt download

RS DesignSpark on Twitter: "#OnThisDay in in 1995 Dan Farmer and Wietse Venema released the Security Administrator Tool for Analyzing Networks, known by its acronym, SATAN, to the Internet. SATAN was a

Odisseus on Twitter: "Inside new #IoT #botnet: #Satan #Roses with #Huawei and Telnet scanners. hxxp://185.101.105.148/shitty.sh hxxp://185.101.105.148/roses.mips roses.arm4 roses.arm5 roses.arm6 roses.i586 roses.mipsel roses.mk68k roses.ppc roses.sh4 ...

Bugs SATAN scans for It is interesting to look at the bugs SATAN scans for. They are easily detected by the scanners and therefore do not pose a threat. - ppt download